5 Important Lessons From GDPR 101 Essex
- Anthony
- March 21, 2018
- 12:53 PM
- No Comments
Fraud, social engineering and more were high on the agenda.
Following the success of its first GDPR 101 event in Hampshire, TMB headed to the Weston Homes Community Stadium in Colchester, Essex, to further spread the word about General Data Protection Regulation and cyber security.
This time, we were joined by David Anthony, Cyber Protect officer at Essex Police. We also heard from Martyn Rochelle of Lloyds Bank’s fraud education team, and Richard Shuker, TMB’s own technical director.
Here are five important lessons from the day.
1. Insider Threat Is Real
Both Martyn and David spoke about the dangers of insider fraud – i.e. fraud committed by people within your own organisation. This could be current employees, but it could also be people who no longer work for you. As David told the audience, it’s an absolute necessity to revoke computer and network access from ex-employees – and to do it promptly. Change their passwords, take back equipment that belongs to the company and so on.
In one case, he said, a recently fired employee still had his work computer, and none of his passwords were changed. Using the information he had, he deleted important company data, posted a lewd image on the business website and changed others’ passwords. Fortunately, he was arrested, but the damage that could be done in such a case could be permanent, and if the personal data of your customers were deleted, for example, it could be your business that’s held responsible under the rules of GDPR.
2. There Is No One-size-fits-all Answer
We had a couple of questions from the audience about data retention times and passing on of data to third parties. While GDPR does address both of these, how you apply the rules is not set in stone, but rather changes on a case-by-case basis.
With data retention, how long you keep the personal data you have depends on what you’re using it for, what kind of permission you have, how it affects the rights of the individual and so on. As the ICO says, GDPR “does not set out any specific minimum or maximum periods for retaining personal data” but it “shall not be kept for longer than is necessary.” Reviewing what data you hold on an annual basis may be a good idea, although the ICO doesn’t specify how often you should do this.
As for the passing on of data, again there’s no single answer. If you have consent from individuals to pass on their data to a third party, then that would be one obvious way to justify it. But there are other lawful reasons to share data with third parties, even without consent. If a third party requests personal data that you hold, they may have legitimate interests that mean it’s okay to share that information. Even then, it’s a matter of weighing up their interests against the rights of the individual, and you should only share information that is strictly relevant.
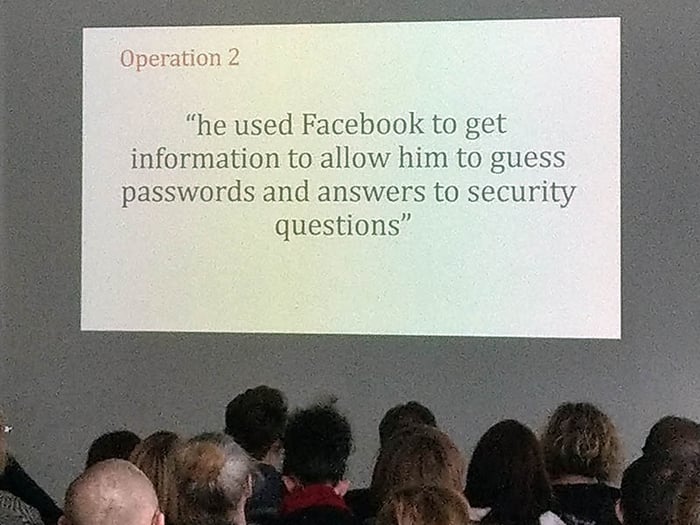
3. Social Engineering Is A Major Threat
As the recent controversy surrounding data mining company Cambridge Analytica has proven, one of the best ways to get personal information from people is to trick them into giving it to you willingly.
That’s what’s social engineering is about. And it’s not just social media sites that are a risk. Criminals also use these tricks via email, phone calls and even in person.
From a GDPR perspective, falling for a social engineering scam could lead to a devastating data breach, which could then possibly lead to a punishment from the ICO.
But that could be the least of your problems. You might also have to deal with ransomware, stolen financial details, invoice fraud and more. Plus any downtime your business experiences would be money lost. In some cases, that’s been enough to finish businesses off completely.
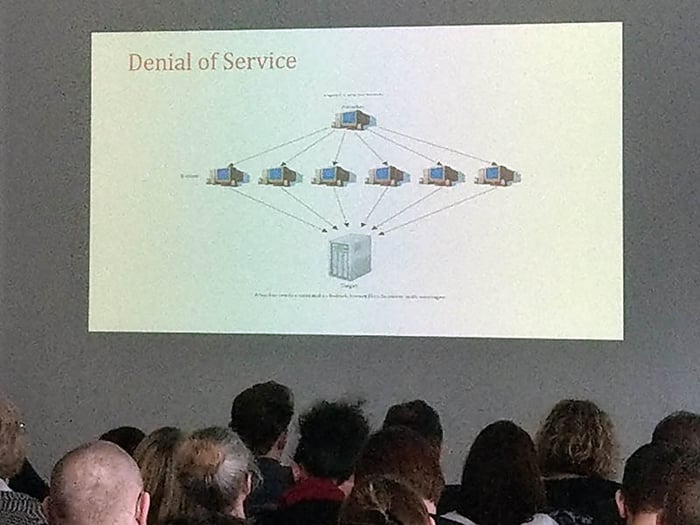
4. Your Own Computers Might Be Attacking Others
When malware finds its way onto your organisations computers, spreading via your local network, it might not necessarily attack you directly. Instead, it could take control of your systems, silently using their computing power to attack other businesses.
Criminals often use huge networks of compromised computers, adding them to what are called ‘botnets’. These botnets might send out spam emails, including phishing mails, or they might launch distributed denial of service (DDoS) attacks. In a DDoS attack, a website will be flooded with requests to access a page. The sheer number of simultaneous requests will cause that website to crash, at which point the criminals may ask for a ransom to end the attack.
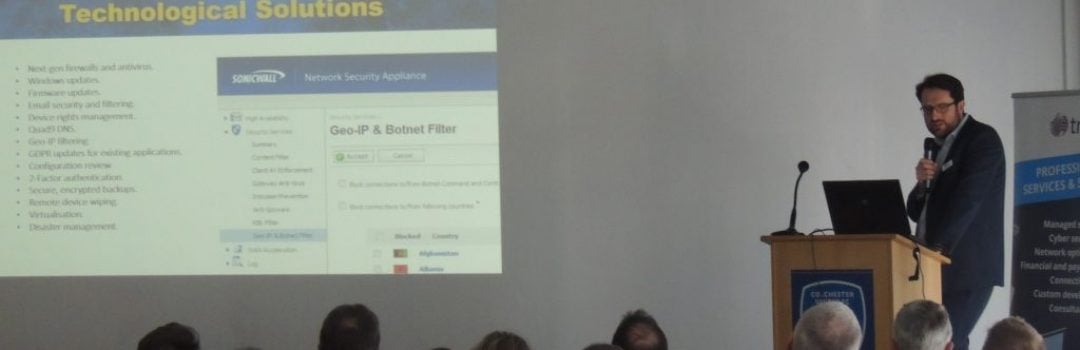
5. Cyber Essentials Is A Great Starting Point
Both Richard and David spoke about the benefits of the Cyber Essentials scheme. This government-endorsed cyber security assessment is affordable and well recognised, making it the ideal starting point for small- and medium-sized businesses.
By checking their security measures and practices against the requirements of the scheme, businesses and other organisations can get a clear picture of what they’re doing right and where they might need improve.
As Richard explained, TMB’s accreditation body offers £25,000 of automatic cyber insurance with every Cyber Essentials certification, and third-party insurers have been known to offer lower premiums for those who are certified.
Furthermore, if you were to suffer a data breach, the ICO would no doubt take your Cyber Essentials certification into account, because it shows you were taking the right kind of precautions, despite the breach.