7 Important Lessons From GDPR 101 Hampshire
- Anthony
- February 7, 2018
- 10:30 AM
- No Comments
What did we learn from TMB's data security seminar?
This week, TMB played host at the Langstone Hotel on Hayling Island, welcoming attendees to its GDPR 101 seminar. As well as our very own technical director, Richard Shuker, we were joined by Martyn Rochelle of Lloyds Bank, and Lucy Dibdin and Stephen Webber of Hampshire Constabulary.
Throughout the morning, we heard about the security implications of the new legislation, and how to avoid the major threats that could lead to data loss or theft.
Here are just seven of the big lessons from the day.
https://youtu.be/ix9V080hYi4
Data Has Value
GDPR places great importance on personal data for a reason: like many things, it's a commodity. Marketers and research companies buy and sell it for legitimate purposes all the time. But it's also of great interest to criminals, who use it to steal from businesses and individuals. Anyone with the will to do so can visit a black market site on the dark web and buy long, long lists of personal and financial information, which has been pilfered by hackers. Using this data, they can commit all kinds of fraud, nearly all of which will leave victims and financial institutions out of pocket.
 Stephen Webber and Lucy Dibdin of Hampshire Constabulary
Stephen Webber and Lucy Dibdin of Hampshire Constabulary
Cyber Crime Is Easy
With so much money to be made from cyber crime, it's perhaps unsurprising that it's run, in many ways, like a legitimate business. There are skilled coders at the top, who produce software applications that are designed to facilitate crime, and there are lesser-skilled criminals who buy those tools and use them to commit the crimes in question. In some cases, they make ongoing payments to the coders, rather than buying the tools outright. What's key is that they don't have to be particularly knowledgeable about technology; they just run the tools and let them do their work. These criminals are also generally young people. As Lucy and Stephen pointed out, the average age of these 'script kiddies' is just 17.

Email Is The Biggest Threat
By far, the greatest source of security breaches is email. According to the government's Cyber Security Breaches Survey, email accounts for 72% of all security breaches among UK businesses. As well as phishing and spearphishing emails, which trick unsuspecting staff members into divulging sensitive information, email can also be a source of dangerous web links. Clicking on these can take you to websites that download malware, which can install viruses or take over your computers. They might also install ransomware, which will encrypt your data and make it inaccessible. And, of course, email allows for attachments, and those, too, can be a source of malware and other nasties.
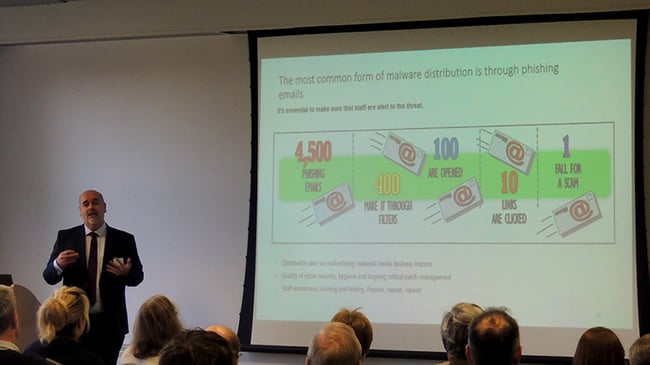 As Martyn Rochelle of Lloyds Bank explained, the sheer number of scam emails is what makes it such a threat
As Martyn Rochelle of Lloyds Bank explained, the sheer number of scam emails is what makes it such a threat
ICO Fines Will Not Be The Norm
If you suffer a cyber security breach and it results in the theft or loss of personal data about customers, staff and so on, then you need to record that and report it to the Information Commissioner's Office (ICO). That's one of the most important aspects of GDPR.
But just because you suffer a data breach, that doesn't mean you're going to be in trouble with the ICO. Quoting the Information Commissioner, Elizabeth Denham, Richard reminded the audience at GDPR 101 that fines will be the last resort. The ICO isn't setting out to punish businesses. Although it is being given greater punitive powers under GDPR, education is at the heart of the ICO's plans.
Invoice Fraud Can Be Devastating
Martyn Rochelle stressed the role of social engineering in fraud. He highlighted invoice fraud as a particularly damaging form of this crime. This is involves criminals impersonating suppliers of a business, usually via email. They claim that they've changed bank accounts, so invoices will have to go to a new account. Then, when the invoice is paid, the money goes to the criminals rather than the supplier. By the time they realise they've been duped, the money is long gone, and there's little chance of recovering it.

Business-related Information Is Part Of GDPR
Do business-related details count, one audience member asked during the GDPR 101 Q&A session. The answer, as Richard explained, is yes, it does, if it identifies, an "identifiable natural person". So john.smith@business.com is covered by GDPR. What about something like ceo@business.co.uk? On the face of it, that's okay, because it doesn't identify an individual. However, if you have other data in your possession, which states that the CEO of Business.com is John Smith, then the CEO email counts as personal information and would be covered by GDPR.
 TMB's Richard Shuker explains the thinking behind GDPR
TMB's Richard Shuker explains the thinking behind GDPR
Some Simple Steps Can Really Help
Cyber crime is changing all the time, becoming ever more sophisticated. But so too are the solutions to fight it. There are many technologies that can help battle cyber crime – technologies that IT specialists like TMB can help with.
However, there are also some much simpler steps that all businesses can take to become more secure. Completing Cyber Essentials certification, for example, can help you get a better understanding of your current cyber security, so you'll be able to see where you're doing well and where, perhaps, you need to improve.
On top of that, just by being more vigilant when it comes to your email, you can massively reduce the risks to your business.
GDPR 101 Essex
Following the success of this event, TBM will holding a another GDPR 101 seminar on 2oth March in Colchester. To book your free spot, head to our registration page and click the Register button.
GDPR Reading List
The ICO Website
The official website of the Information Commissioner's Office is the perfect place to find out about all aspects of data protection and GDPR. Particularly useful are the Guide to the General Data Protection Regulation (GDPR) and advice for small organisations.
Microsoft
Microsoft is doing a number of things to help businesses with GDPR, including providing a free GDPR assessment
Intersoft Consulting
Here, you'll find the official GDPR document laid out as a searchable website.
https://gdpr-info.eu/ - the information from the official PDF, laid out as a website.
GDPR - Fix it Fast: Apply GDPR to Your Company in 10 Simple Steps
This book, by Patrick O'Kane could be handy if you need an offline guide to GDPR.
The Ultimate GDPR Practitioner Guide: Demystifying Privacy & Data Protection
Another option if you're after a GDPR book is this one by Stephen Massey .