Cyber Security & The Supply Chain
- Anthony
- November 1, 2019
- 09:45 AM
- No Comments
It's not just your own defences you should be concerned about.
Taking care of your own cyber security should be your priority, but breaches suffered anywhere in your supply chain can cause your business problems.
As the metaphysical poet John Donne once wrote, "No man is an island". The same can be said for businesses. Whether your organisation is a huge multinational, a one-man band or anything between, it doesn’t function in isolation; at some point, you have to rely on other businesses.
Below is an example of a basic supply chain. Real-life chains may be much more complex than this, but for simplicity’s sake, this graphic will suffice.
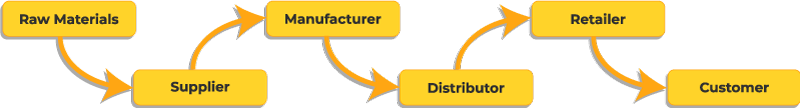
The main point is that no matter where your business sits in the chain, you will have some kind of dependency on other businesses. That has major implications in terms of cyber security, because if one of them is disrupted, this can result in a ripple effect throughout the rest of the chain.
Let’s say you own a factory that makes chocolate biscuits. You get your ingredients from a variety of suppliers – one provides you with flour, another with sugar, and yet more sell you things like butter and chocolate. If just one of those suppliers suffers a problem, such as a ransomware attack that prevents it processing orders, the supply chain can can be severely disrupted. Without chocolate, for example, you can’t make chocolate biscuits.
The knock-on effects should be clear. If you can’t make your product, you can’t supply your distributor, the distributor can’t supply the retailer, and the final customer (the consumer) doesn’t get the chocolate biscuit – at least not one made by your company.
The ripple effect doesn’t only move forward either. While you’re unable to get chocolate, you might also pause or slow your orders of other ingredients. Your suppliers may then, in turn, do the same with raw material providers.
Of course, businesses may have processes and backup plans to account for problems like this. Your chocolate biscuit factory, for instance, could use multiple chocolate suppliers or keep a backup reserve of chocolate. Your distributors, too, might keep reserves.
But, on the other hand, you might not do these things. Instead, you might use only one supplier for a particular product, and it might not be practical or affordable to keep excess stock. Or you might subscribe to a 'just in time' manufacturing methodology that eschews stockpiling, in favour of ordering just enough, just at the right time it's needed. In that case, a major cyber attack anywhere in your supply chain could have significant consequences for your business operations and for your bottom line.
And while the focus of this post is disruption of supply, it's not the only threat you might face. Your supply chain can make your own business vulnerable to attack as well. Someone who hacks a business partner of yours could access all the data they have on your company, which they could then use to hack your systems or send you phishing emails. Criminals may also intercept invoices from suppliers and replace them with forgeries. And websites and files may be altered to spread malware throughout the chain.
Is there actually anything you can do about it, though? Maybe. While you can’t directly dictate what other businesses do in terms of their cyber security, you might use it as a stipulation in your dealings with them. Your contracts might, for example, be dependent on suppliers having at least basic security measures or a Cyber Essentials certification.
If you’re particularly concerned, you could even offer exclusive prices and rates for firms that meet your security demands.
Just talking about cyber security can helpful too. Discuss with your suppliers and distributors what you’re doing to protect your own business. Share tips and ideas about security. Find out if they’re doing anything that you could be doing too. Anything that keeps the conversation going and reminds them that cyber security is important.
Ultimately, it’s up to each organisation to make sure its security is adequate, but everyone has to play their part. If any businesses you work with aren't taking cyber security seriously enough, it might be worth considering alternative arrangements.